Imagine you want to send a document over the internet and know instantly if someone tampered with it. You can't physically see changes to binary code. That is why we rely on cryptographic hashing. It acts as a unique digital fingerprint for every piece of information. Without this technology, blockchains would just be vulnerable databases that anyone could alter.
In simple terms, cryptographic hashing is a mathematical function that converts any input data into a fixed-size string of characters representing that data uniquely. This process creates a digital signature that cannot be reversed. When you hear people talk about Bitcoin mining or securing transactions, they are mostly talking about this exact mechanism at work.
The Mechanics Behind the Magic
To understand why this matters, you need to grasp how it behaves under pressure. A standard hash function might look random, but cryptographic versions have strict rules. First, it is deterministic. If you feed the same input into the system twice, you get the exact same output every time. Second, it produces a fixed output regardless of input size. Whether you enter a single letter or an entire novel, the resulting hash remains the same length.
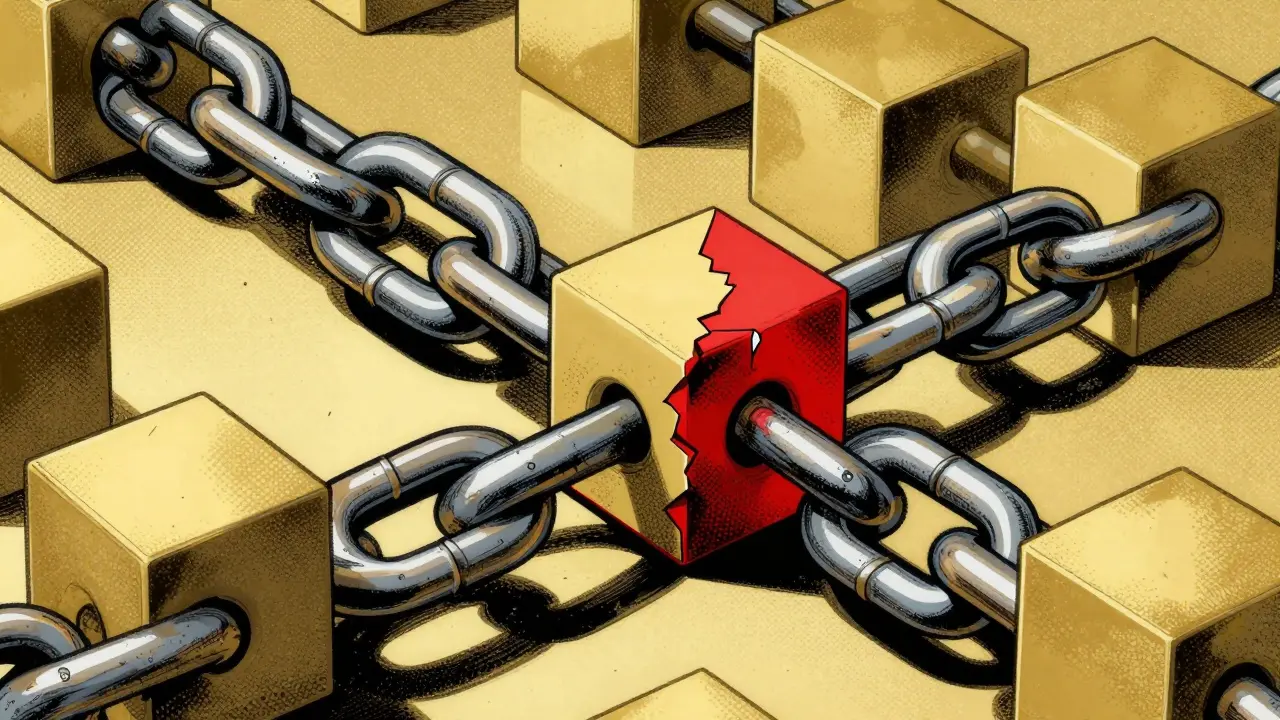
This consistency is vital for verification. Consider the blockchain. This distributed ledger technology relies on linking blocks of data through their respective hash values to ensure historical records remain unchangeable. If someone tries to change a transaction inside an old block, the hash for that block changes immediately. Because the next block contains the hash of the previous one, the chain breaks. Everyone in the network sees the mismatch and rejects the alteration.
We also need to talk about the avalanche effect. This sounds dramatic, but it describes how sensitive the system is. Change just one bit of the input data, and roughly 50% of the output bits will change. There is no way to predict which bits will flip. This makes it nearly impossible to guess an input based on its hash output. It essentially creates a one-way street for information.
Why Blockchains Cannot Function Without It
You might wonder why regular checksums aren't enough. Traditional checks catch accidental errors, like a corrupted file download. But they do not stop malicious attacks. In a decentralized environment, there is no central authority to police the data. You need math that enforces trust instead of a person.
The core value proposition lies in creating an immutable, tamper-evident ledger. Each block contains the hash of its own data, the timestamp, and the hash of the previous block. This structure forces a sequential dependency. As documented by industry experts, altering any block requires recalculating the hashes for that block and all subsequent blocks. On a network like Bitcoin, the original cryptocurrency that popularized blockchain technology and uses SHA-256 for its proof-of-work consensus mechanism, the combined computing power of the global network makes this computationally infeasible.
This setup ensures data integrity without needing a third party. You do not need to trust a bank; you trust the mathematics. The security model assumes that attacking the network would cost more than the potential gain. For instance, reversing a single day of Bitcoin transactions would cost approximately $1.2 billion at current rates. This economic disincentive is built directly into the hashing mechanism.
Common Algorithms in Play
Not all hashes are created equal. Different projects choose different functions based on their needs for speed, security, or energy efficiency. The most famous one is SHA-256. It generates a 256-bit hash, displayed as 64 hexadecimal characters. It is widely adopted because it has survived years of scrutiny without successful collisions.
However, newer platforms often use alternatives. Ethereum, a smart contract platform that utilizes Keccak (SHA-3) variants for state management and transaction processing, shifted away from pure mining competition after its transition to proof-of-stake. Still, it keeps hashing for data integrity. Other systems prefer BLAKE2 for faster software performance. Let's compare the big players to see why the choice matters.
| Algorithm | Primary Use Case | Output Size | Speed |
|---|---|---|---|
| SHA-256 | Bitcoin Mining & Verification | 256 bits | Moderate |
| SHA-3 | Ethereum State Updates | 224-512 bits | Faster Software |
| BLAKE2b | Nano, Polkadot | Up to 512 bits | Very Fast |
| Ripemd160 | Wallet Addresses | 160 bits | Legacy Support |
SHA-256 dominates hardware optimization. Specialized chips, called ASIC miners, perform billions of calculations per second. This creates high security but also high energy consumption. SHA-3 offers better resistance to certain theoretical attacks but runs slower on standard CPUs. BLAKE2 provides a sweet spot for software-heavy platforms that do not require dedicated mining hardware.
Real-World Application and Verification
Theory is great until you try to run a node. Practical implementation reveals nuances like endianness issues. Developers often spend days debugging why a hash calculation fails across different systems. Binary representations matter immensely. A difference between big-endian and little-endian byte ordering can cause a hash mismatch, leading to rejection of valid blocks.
When you run a Bitcoin node, it constantly verifies the Merkle tree roots. These trees organize transaction hashes into hierarchical structures. This design reduces verification complexity significantly. Instead of downloading megabytes of transaction data, a lightweight wallet can prove a transaction exists using only a tiny fraction of the data. This allows mobile devices to interact with the blockchain securely without storing the full history.
Verification times are incredibly fast. Average verification sits around 0.00015 seconds per transaction. This speed allows for high throughput even when security requirements are stringent. Enterprise users report private blockchain implementations achieving faster finality with specific hash choices compared to public chains. The technology moves beyond just coins; it secures supply chains and identity records too.
Future Challenges and Quantum Risks
Nothing lasts forever in computer science. The biggest concern looming over current standards is quantum computing. While traditional computers take centuries to crack SHA-256, a sufficiently powerful quantum machine could theoretically reverse hashes much faster. Estimates suggest a processor with 1,500+ qubits could pose a threat, though such machines do not exist yet.
Organizations like NIST are already working on Post-Quantum Cryptography standards. They aim to define hash-based signatures that resist these quantum attacks. Hybrid approaches combining traditional hashing with new techniques are likely the path forward. Long-term viability depends on upgrading protocols before quantum hardware catches up. Experts estimate we have until the mid-2030s to prepare, giving the ecosystem time to migrate safely.
Wrapping Up the Concept
Cryptographic hashing is the engine room of blockchain technology. It is the silent worker ensuring that your transaction record matches what everyone else sees. It handles security tasks without relying on trust between strangers. From the earliest days of Satoshi Nakamoto to modern enterprise ledgers, this math remains the foundation of digital ownership.



joshua kutcher
April 1, 2026 AT 01:01Understanding how the avalanche effect works is crucial for anyone serious about blockchain security. It is wild how changing a single letter completely obliterates the output hash in a way that looks random. Without that property we would not have secure ledgers like Bitcoin functioning today. People often forget that the math is what holds the whole thing together instead of trust in a bank. I have seen so many projects fail because they implemented their own custom hashing logic without auditing it properly. That is usually where vulnerabilities creep into the system unnoticed until it is too late. We need to remember that standard algorithms like SHA-256 have survived decades of cryptanalysis attempts. There is comfort in knowing that the community has already stress tested these functions extensively. It also makes verification incredibly fast which is great for scaling solutions eventually. I appreciate how you highlighted the difference between checksums and cryptographic hashes early on. That distinction saves so much confusion for newcomers entering the space. Many people think data corruption is the same as malicious tampering but the tools differ wildly. Sticking to established standards is always the safer route for enterprise adoption too. We should encourage more developers to read the raw specs before using libraries blindly. It helps build a stronger foundation for everyone working in distributed systems. Keeping protocols updated is the only way to stay ahead of new attacks constantly.
Justin Garcia
April 1, 2026 AT 10:32Investors rarely care about these deep mechanics when prices drop.
Shubham Maurya
April 2, 2026 AT 12:40You are totally missing the point of why infrastructure matters 💀💻 Security doesn't show up on your portfolio but without it everything crashes 🔥 Stop being so negative about the tech 🚀
athalia georgina
April 2, 2026 AT 19:01I tryed running a node last week and honestly the endianess bugs were driving me crazy 😓 It is nice to see someone explaining the big picture here tho. My server kept rejecting valid blocks cause i forgot the byte ordering rules again. Maybe its just me being new but debugging hash mismatches is soo tedious sometimes. Thanks for posting this info it clears things up a bit for the rest us learning devlopment.
Elizabeth Akers
April 3, 2026 AT 02:49totally agree with the mentoring vibes here love the explanation about audit trails. standard algo stuff is definitely key for anyone serious about building stuff though. quantum risk is scary but lets see how time goes with nist updates. good writeup overall