The Crypto Spectrum News - Page 2

What is Ethernity CLOUD (ECLD)? A Deep Dive into the Token and Risks
Explore Ethernity CLOUD (ECLD), a crypto token for private cloud computing. Learn about its tech, risks, and market performance.
Are Crypto Payments Allowed in Nigeria? 2026 Legal Status & Rules
- 6 Comments
- May, 21 2026
Crypto payments are legal in Nigeria under the ISA 2025, though not legal tender. Learn about SEC licensing, CBN bank guidelines, and the new 2026 tax rules for traders.

Osmosis Crypto Exchange Review: The Best DEX for Cosmos in 2026?
A detailed review of Osmosis, the leading decentralized exchange for the Cosmos ecosystem. We analyze fees, security, features, and how it compares to Uniswap and PancakeSwap in 2026.

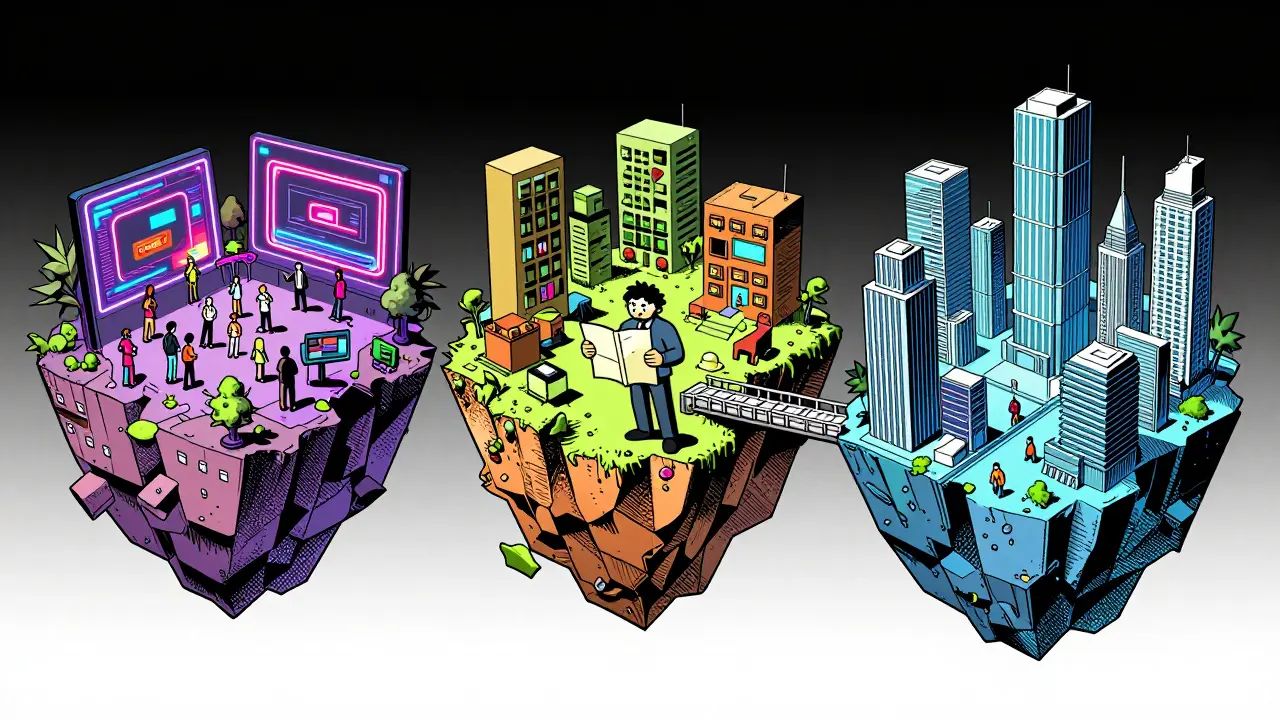
Choosing the Best Crypto-Friendly Jurisdiction for Your Blockchain Business in 2026
Choosing the right crypto-friendly jurisdiction impacts taxes, compliance, and banking access. Compare UAE, Switzerland, Singapore, Cayman Islands, and Bermuda for your blockchain business in 2026.
Metaverse Real Estate Investment: A 2026 Guide to Virtual Land
Explore metaverse real estate investment in 2026. Learn about virtual land risks, top platforms like Decentraland and The Sandbox, and proven monetization strategies for digital property.
Metaverse Real Estate Investment: A 2026 Guide to Virtual Land
Explore metaverse real estate investment in 2026. Learn how to buy virtual land, top platforms like Decentraland, and monetization strategies for digital property.

Swaperry IDO Airdrop: How to Claim Tokens and Avoid Scams
- 9 Comments
- May, 17 2026
A comprehensive guide to the Swaperry IDO promotion and airdrop. Learn how to verify legitimacy, avoid scams, and safely claim tokens while understanding the risks involved.

LMAX Digital Crypto Exchange Review: Institutional-Grade Trading for Professionals
LMAX Digital review: A regulated, institutional-grade crypto exchange offering ultra-low fees, FCA/GFSC compliance, and Equinix-hosted speed for professional traders.
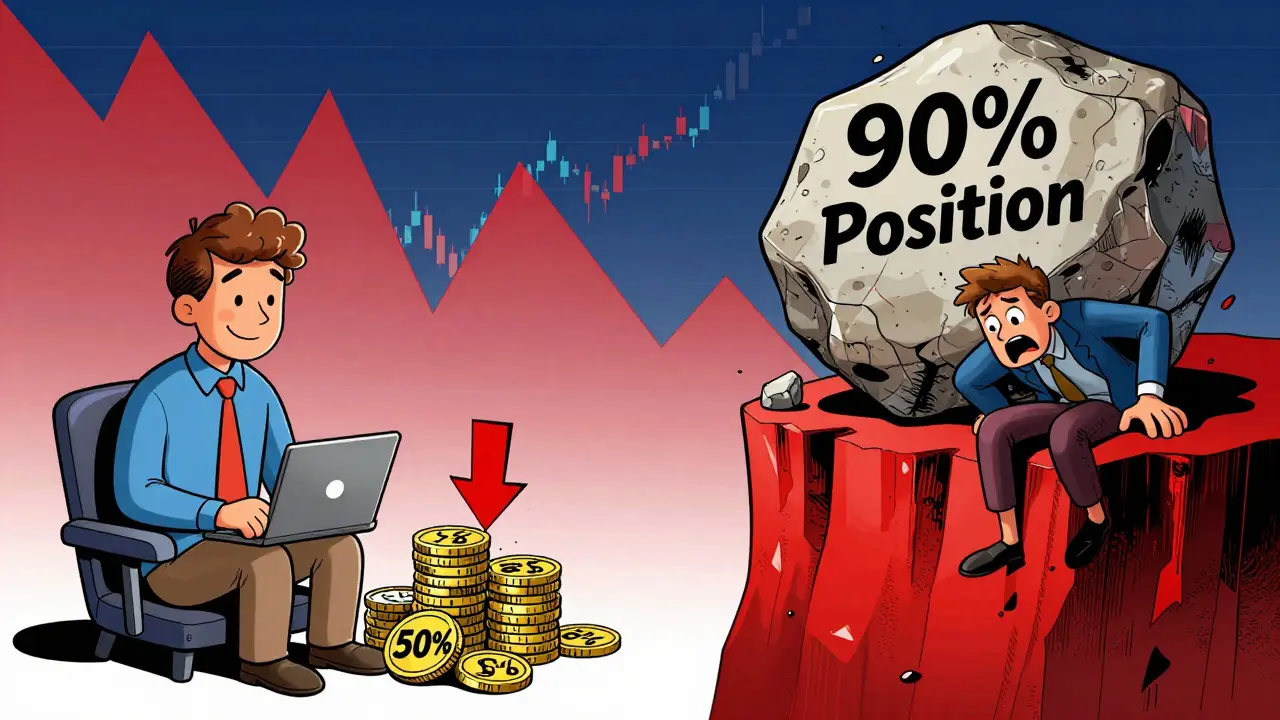
SEC Crypto Fines in 2024: Why Penalties Skyrocketed While Cases Dropped
In 2024, SEC crypto enforcement fines surged by 3,018% despite fewer cases. Discover how Gary Gensler's final year focused on massive settlements, the Howey Test, and strategic litigation to reshape digital asset regulation.

FAN8 Airdrop: Status, Eligibility, and How to Avoid Scams in 2026
- 9 Comments
- May, 14 2026
There is no official FAN8 airdrop in 2026. Beware of scams using the FAN8 name. Learn how to spot fake claims, avoid wallet drains, and find legitimate crypto opportunities instead.

What is Arkimals (EGG) Crypto? Token Utility, Price, and Risks
Arkimals (EGG) is a micro-cap gaming token on the Waves blockchain used for breeding NFT animals. With minimal liquidity and high volatility, it poses significant risks for investors despite its play-to-earn utility.
How Composability Drives DeFi Innovation: The Power of Money Legos
Explore how DeFi composability, known as Money Legos, drives innovation by enabling seamless protocol integration. Learn about the benefits, risks, and future of composable finance.